Sonic price prediction 2026-2032: Will S reach $1 soon?
Key takeaways:
- The average Sonic price prediction for 2026 is $0.03259.
- Holders can anticipate a maximum price of $0.1574 in 2029.
- By 2032, Sonic (S) might touch $0.2967
Sonic is a high-performance EVM Layer 1 blockchain built for DeFi applications, offering up to 400,000 TPS and sub-second finality. The network introduced its Fee Monetization (FeeM) program, allowing developers to earn up to 90% of the fees generated by their applications. Sonic also features a native Ethereum bridge called the Sonic Gateway, which includes a Fast-Lane transaction feature and a fail-safe security mechanism. For investors and traders following Sonic price prediction trends, these features are important because they support ecosystem growth, developer activity, and the chain’s long-term demand.
Sonic emerged from Fantom’s rebrand after Michael Kong announced the Sonic mainnet launch in March 2024. Fantom later fully transitioned to Sonic on January 16, 2025, as the project expanded through partnerships with Chainlink, Pyth Network, Alchemy, Dune, and Safe.
Sonic reached an all-time high of $1.03 in January 2025 before falling to a low of $0.0368 in February 2026. Investors’ questions remain. Will Sonic reclaim Fantom’s all-time high of $3.48? How high can Sonic (S) go in the coming years? Let’s take a look at Sonic’s price prediction and price prediction tool to answer these questions.
Sonic Price Prediction: An Overview
| Cryptocurrency | Sonic |
|---|---|
| Token | S |
| Price | $0.02906 |
| Market Cap | $83.71M |
| Trading Volume (24-hour) | $19.27M |
| Circulating Supply | 2.88B S |
| All-time High | Jan 05, 2025 $1.03 |
| All-time Low | Jun 05, 2026 $0.03036 |
| 24-h High | $0.040901 |
| 24-h Low | $0.040163 |
Sonic (S) price prediction: Technical analysis
| Volatility | 4.09% (Medium) |
|---|---|
| 50-Day SMA | $ 0.04407 |
| Price Prediction | $ 0.02376 (-25.50%) |
| 14-Day RSI | 37.59 (Neutral) |
| Green Days | 11/30 (37%) |
| Sentiment | Bearish |
| Fear & Greed Index | 12 (Extreme Fear) |
| 200-Day SMA | $0.06032 |
Sonic price analysis S falls to a new all-time low as sellers stay in control
TL;DR Breakdown
- Today’s Sonic price analysis shows strong bearish pressure as S falls to a fresh all-time low of $0.02768
- Sonic’s current resistance is at $0.0321, while the immediate support remains at the all-time low of $0.0277
- Today, Sonic is trading around $0.02924, down 6.32% in the last 24 hours
As of June 6, 2026, Sonic’s price analysis shows a bearish market structure. Sonic is currently trading at $0.02928, down 6.32% in the last 24 hours. Selling pressure increased today, driven by Sonic’s new all-time low price of $0.02768, underscoring the continued market dominance by bears. Although buyers managed to trigger a small recovery from the lows, it remains weak as the price continues to trade near historically depressed levels.
Sonic (S) price analysis 1-day chart
Analyzing the one-day chart for Sonic, it shows persistent selling pressure after the token recorded a fresh all-time low.S dropped to $0.02768, breaking below previous support levels and extending its broader downtrend that has been in place for several months.
The latest daily candle remains bearish despite a small recovery from the day’s low. The decline reflects weak market confidence, with sellers continuing to dominate price action. Sonic is now trading more than 97% below its all-time high of $1.03, showing the level of the long downtrend.
Trading activity has weakened over the past 24 hours, with volume falling by 26.14% to $18.93 million. The decline in volume suggests that market participation is cooling despite Sonic’s drop to a new all-time low, indicating limited buying interest at current levels.

Technical indicators continue to favor sellers. The Relative Strength Index (RSI) has dropped to 21.9, placing Sonic deep in oversold territory. While such levels often precede temporary relief rallies, the indicator is yet to show any meaningful bullish divergence. The continued decline in RSI reflects strong bearish momentum and weak buying interest.
The MACD indicator remains negative as the MACD line trades below the signal line. Expanding red histogram bars suggest that downward momentum is still dominating the market despite today’s rebound from the all-time low. This setup indicates that sellers continue to control the broader trend.
Buyers need to reclaim the $0.0320 area before any meaningful short-term reversal can be considered. Until then, rallies may continue to attract selling pressure.
S’s technical analysis 4-hour chart
The 4-hour Sonic price chart shows bears still maintaining strong control of the market. Although the token has stabilized around the $0.0294 level, buying momentum remains weak as the broader trend continues to favor sellers.
The RSI on the 4-hour timeframe has dropped to 20.17, still in oversold territory. While this suggests selling pressure has become extreme, the indicator has yet to show a convincing recovery signal. The MACD indicator remains bearish.

The MACD line continues to trade below the signal line, confirming that downward momentum is still dominant. However, the shrinking red histogram bars suggest that bearish momentum is beginning to slow, although buyers have not yet gained enough strength to reverse the trend.
The nearest resistance is at $0.0300, followed by a stronger barrier around $0.0320. On the downside, immediate support remains at the recently established all-time low of $0.02768. If bears force a break below this level, Sonic could face another low as price discovery continues.
Sonic technical indicators: Levels and action
Daily simple moving average (SMA)
Moving averages are calculated from the average closing price over a set period.
| Period | Value | Action |
|---|---|---|
| SMA 3 | $ 0.03570 | SELL |
| SMA 5 | $ 0.03739 | SELL |
| SMA 10 | $ 0.03926 | SELL |
| SMA 21 | $ 0.04228 | SELL |
| SMA 50 | $ 0.04407 | SELL |
| SMA 100 | $ 0.04316 | SELL |
| SMA 200 | $ 0.06032 | SELL |
By June 29, 2026, Sonic’s 200-day Simple Moving Average is projected to drop to $0.05181, while the 50-day SMA is estimated to reach $0.03714.
Daily exponential moving average (EMA)
| Period | Value | Action |
|---|---|---|
| EMA 3 | $ 0.03547 | SELL |
| EMA 5 | $ 0.03674 | SELL |
| EMA 10 | $ 0.03885 | SELL |
| EMA 21 | $ 0.04130 | SELL |
| EMA 50 | $ 0.04328 | SELL |
| EMA 100 | $ 0.04941 | SELL |
| EMA 200 | $ 0.08657 | SELL |
What can you expect from the Sonic price analysis next?
Sonic remains in a corrective trend, but Sonic’s price action is showing early signs of stabilization around the $0.0290 level, and many traders use candlestick charts to assess momentum. Each candlestick shows the opening, closing price, highest, and lowest prices for a chosen interval, helping analysts determine whether support is holding or a rebound may follow.
A successful defense of the $0.02768 support level could allow the token to recover toward $0.0300 and potentially $0.0320 in the coming sessions, according to Sonic key price levels and recent market activity. On the downside, a break below the all-time low of $0.02768 would likely expose Sonic to further weakness, with sellers attempting to establish new lower levels.
In a relatively small market, whales can control short-term moves. Until buyers reclaim the $0.0300–$0.0320 resistance zone, the overall market structure remains bearish despite oversold conditions appearing on technical indicators.
Why is Sonic down today?
Sonic (S) is trading around, down 12.44% over the last seven days, suggesting the broader trend remains bearish despite today’s modest recovery. With no major news catalyst driving recent price action, the decline appears to be due to typical altcoin volatility and profit-taking following earlier gains.
Is Sonic a good investment?
Sonic is a high-speed, scalable blockchain platform that competes with established chains such as Solana and Ethereum L2s, positioning itself as a performance-focused chain within the blockchain ecosystem. Despite its potential, investing in Sonic (S) involves risks typical of cryptocurrencies, including market volatility, so any current forecast should weigh whether it looks like a good buy right now.
While Sonic does not currently lead the market, it maintains a credible and stable position as a reliable, mid-tier chain. Sonic (S) network is also transitioning from a community-driven layer-1 to a more structured corporate model, which investors should factor in before they invest. Own research and assessing personal risk tolerance are essential for anyone considering S as a potential investment opportunity.
Will Sonic reach $5?
The price of Sonic could reach $0.1215 by 2030, with price predictions suggesting a high of $0.1678. The base case scenario for Sonic’s price by 2030 is projected to be around $0.1215, with potential highs depending on market conditions. However, achieving this depends on market conditions, overall technical factors, and fundamental factors.
Will Sonic reach $10?
Based on our technical analysis of multiple technical quantitative indicators, S’s price projections for 2032 estimate a range, with Sonic expected to reach about $0.2967 but not approach double-digit prices within the next 6 years. A move to $10 is not guaranteed; even by 2046, Sonic is expected to reach $0.8797, still far below $10 and requiring over 25,386% upside to hit that mark.
Is Sonic a safe network?
Sonic is regarded as a secure blockchain platform whose architecture differs from traditional blockchains, using its unique Lachesis consensus mechanism to enable high-speed, scalable transactions.
Its directed acyclic graph approach helps deliver theoretical throughput of up to 10,000 transactions per second with finality in less than 500 milliseconds. However, as with any blockchain network, users should exercise caution, use official channels, and follow best security practices to protect their assets.
Does Sonic have a good, long-term future?
Sonic shows potential for a strong long-term future, with price predictions suggesting significant growth by 2030 and beyond. Analysts forecast prices could reach between $0.1215 and lowest prices at $0.1678, driven by its unique blockchain technology, increasing adoption in decentralized applications, and robust ecosystem growth.
Ecosystem growth, fueled by increased developer activity and more developers joining the platform, is crucial for Sonic’s long-term success. Total Value Locked (TVL) in dApps is a critical metric for long-term growth, reflecting real-world usage and platform strength. Sonic also continues airdrop campaigns and support for liquid staking tokens to help boost TVL and revenue generation.
Additionally, the Sonic ecosystem has established a $25 million fund to attract builders and improve user metrics, further supporting future expansion. Future ecosystem expansion may also benefit from plans to pursue a Spot ETF and private investment vehicles on Nasdaq, though the long-term impact remains uncertain. However, market volatility remains a concern.
Recent news/opinion on Sonic (prev. FTM)
Sonic recently expanded its ecosystem focus through infrastructure and security upgrades, including USDC integration support and new stablecoin functionality via Flying Tulip. The developments aim to strengthen Sonic’s position as a developer-friendly EVM chain while improving on-chain utility and security, even as the token continues facing bearish pressure in the broader crypto market.
Sonic recently highlighted the growing adoption of its vertical integration model. The network revealed that its USSD stablecoin is generating approximately $80,000 in annualized real-world asset (RWA) yield without incentives, while Shadow’s AutoVault has already purchased around 350,000 S tokens through market activity.
Sonic price prediction June 2026
The Sonic price prediction for June 2026 suggests a modest recovery from current levels, with the price expected to range between $0.02881 and $0.03259. The average price is projected to be around $0.03259, as market sentiment, trading volume, and broader crypto market conditions continue to influence short-term price action.
| Period | Potential Low ($) | Average Price ($) | Potential High ($) |
|---|---|---|---|
| Sonic (S) price prediction June 2026 | $0.02881 | $0.03259 | $0.03259 |
Sonic price prediction 2026
In 2026, Sonic (S) is expected to trade between $0.02750 and $0.03789, with an average price of around $0.03270. This suggests relatively stable price action throughout the year, with modest upside potential if ecosystem growth and market sentiment improve.
| Period | Potential Low ($) | Average Price ($) | Potential High ($) |
| Sonic Price Prediction 2026 | $0.02750 | $0.03270 | $0.03789 |
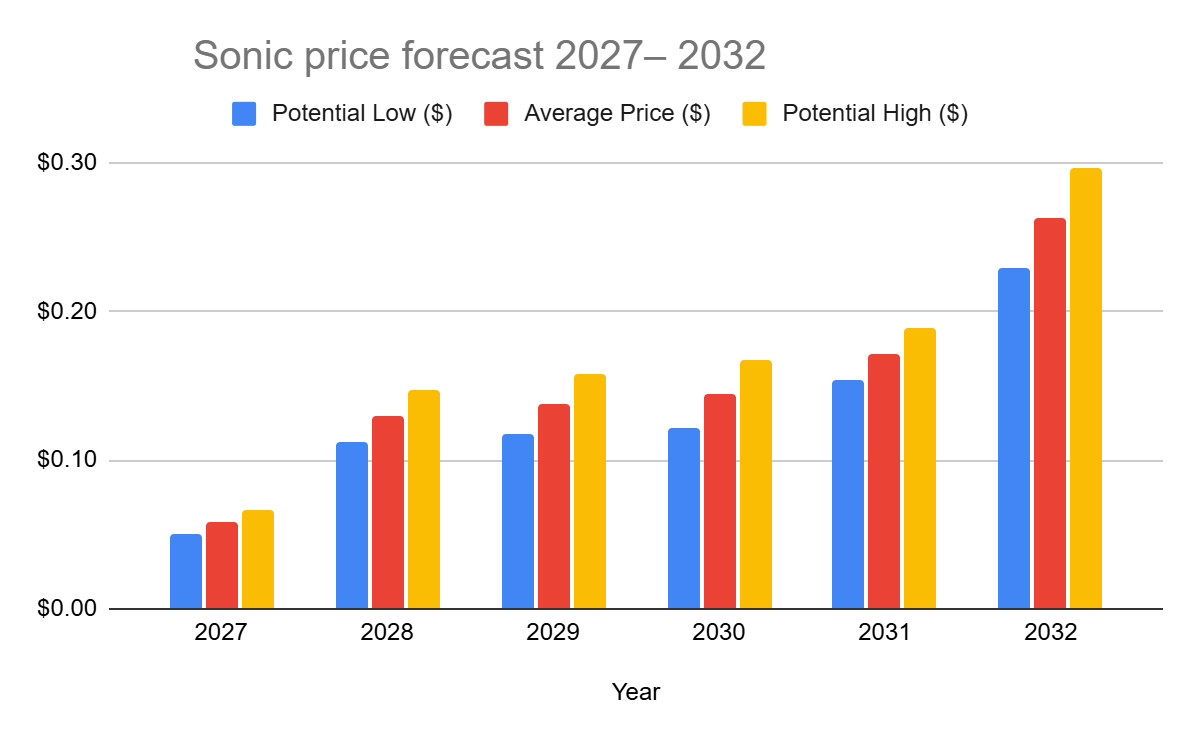
Sonic price forecast 2027– 2032
price prediction chart
| Year | Potential Low ($) | Average Price ($) | Potential High ($) |
| 2027 | $0.0499 | $0.0581 | $0.0662 |
| 2028 | $0.1128 | $0.1296 | $0.1465 |
| 2029 | $0.1169 | $0.1372 | $0.1574 |
| 2030 | $0.1215 | $0.1446 | $0.1678 |
| 2031 | $0.1545 | $0.1717 | $0.1889 |
| 2032 | $0.2285 | $0.2626 | $0.2967 |
Sonic (S) price prediction 2027
The Sonic forecast for 2027 speculates that the price might reach a maximum of $0.0662 by 2027. On the lower end, corrections may pull the price to $0.0499 with an expected average trading price of around $0.0581. As an alternate modeled scenario, the predicted price for 2027 could be around $0.03998, representing a potential 1.90% increase.
Sonic (S) price prediction 2028
Sonic’s (prev. FTM) 2028 forecast of $0.1128–$0.1465, averaging $0.1296, is linked to growing adoption of its rebranded ecosystem. By then, expanded DeFi, NFT, and gaming use cases are expected to strengthen utility and demand. The projected rise in Sonic’s price by 2028 is supported by its Fee Monetization model and the fee burning mechanism, which incentivize developer activity and reduce token supply. Network scalability upgrades and rising developer engagement support gradual appreciation, while market cycles keep growth within range.
Sonic (S) price prediction 2029
In 2029, Sonic’s market price might stabilize at $0.3238 while attaining an average trading price of around $0.2698, and a minimum price of around $0.2158. The broader outlook points to $0.03250 by the end of 2026, $0.1464 by 2030, and $0.2327 by 2040, based on combined technical and fundamental factors.
Sonic (S) price prediction 2030
Sonic is expected to reach a maximum of $0.1678 by 2030. However, it could fall to $0.1215 with an average price of $0.1446.
Sonic (S) price prediction 2031
Sonic is projected to hit a high of $0.1889 in 2031. In the event of a price correction, it could drop to $0.1545 with an average of $0.1717
Sonic (S) price prediction 2032
Sonic is expected to reach a high of $0.2967 in 2032. The average trading price is expected to be $0.2626, and the minimum price is projected to be $0.2285.
Sonic market price prediction: Analysts’ FTM price forecast
| Firm Name | 2026 | 2027 |
|---|---|---|
| Coincodex | $ 0.02589 | $ 0.06573 |
| DigitalCoinPrice | $ 0.03189 | $0.0817 |
It’s important to note that these analyst forecasts may be influenced by broader market rallies and shifts in market sentiment, which can drive Sonic’s price targets higher or lower depending on overall investor optimism or pessimism.
Cryptopolitan’s Sonic (S) price prediction
Our predictions show that the Sonic token could achieve a minimum value of $0.02750 in 2026. The Sonic price may reach a maximum value of $0.03789, with an average trading price of $0.03270 throughout 2026. Investor confidence, along with supply and demand dynamics, plays a key role in Sonic’s price action.
Fundamental events such as hacks and other real-world occurrences can significantly impact price movements. Please note that the content provided on this page is for informational purposes only and does not constitute investment advice. Conduct your own research before making financial decisions
Sonic’s (S) historic price sentiment

- Fantom (FTM) launched in 2018 at $0.0182, hit a low of $0.00229 in 2020, and peaked at $3.24 in 2021 during the DeFi boom.
- Following the 2022 bear market, FTM recovered to $0.55 by early 2024 before rebranding to Sonic Labs in August 2024.
- The 1:1 FTM-to-Sonic (S) token swap began in December 2024, with Binance completing it by January 2025.
- Sonic hit a new ATH of $1.029 in January 2025, but steadily declined to around $0.33 by late August.
- By early September 2025, Sonic traded stably between $0.3092 and $0.3126.
- Early September, Sonic traded around $0.309–$0.313, showing relative stability compared to its August lows.
- Mid-September – Price remained in the ~$0.30–$0.33 band, with minor upward drift toward ~$0.32.
- Late September – The token approached $0.26, as reported by markets, showing a decline and increased volatility.
- Early October – Trading price dropped further into the ~$0.23–$0.26 range, indicating a weakening trend.
- By November 3, Sonic had fallen to approximately $0.122, marking a substantial decline from early September levels.
- At the beginning of November 2025, Sonic (S) traded around $0.12–$0.14, occasionally spiking to roughly $0.17 before retreating.
- Through mid-November, the price generally drifted downward, reaching a low near $0.10–$0.11 around November 21.
- From late November to December 3, S recovered slightly — trading in a narrow band around $0.10–$0.11, suggesting consolidation and stabilization after the mid-month slump.
- From early December, Sonic traded around $0.071–$0.075 on Dec 3–Dec 6, then moved higher through mid-December as the price climbed into the $0.085–$0.095 zone by Dec 14–Dec 17, reflecting increasing buying interest late in the year.
- Into late December and early January, S stabilized in the $0.07–$0.08 range before rising above $0.08, closing around $0.082–$0.086 by Jan 4 2026, showing a modest recovery into the new year.
- On January 4, 2026, Sonic was trading near $0.086–$0.090 after stabilizing from December weakness, with modest rebounds in the first week of January as buyers emerged off key support levels.
- By February 3, 2026, Sonic had drifted lower toward roughly $0.065–$0.070, reflecting continued selling pressure and failed rallies, with price consolidating near the low end of its recent range.
- Sonic (S) traded around $0.052 to $0.048 between Feb 3 and Feb 10, 2026, before declining toward the $0.041 to $0.039 range by late February amid steady selling pressure.
- From early March to Mar 14, 2026, Sonic moved between $0.038 and $0.044 with a gradual rebound attempt as the price stabilized near the $0.040 support zone.
- From March 14 to late March, Sonic drifted lower from $0.0514 toward $0.040–$0.042, unable to sustain any meaningful bounces amid broad market weakness.
- By April 7, its price pressed critical $0.040 support at $0.0396–$0.0414 — dangerously close to its all-time low of $0.0368 set on February 28.
- Sonic is trading at around $0.04951 at the start of May 2026.
- By the end of May 2026, Sonic had retreated to around $0.040, erasing much of its early-May gains after a failed rally above $0.055 and stabilizing near a key support zone amid continued selling pressure.
- At the start of June 2026, Sonic traded around $0.03136, extending its decline after losing the key $0.040 support level in late May.