Cyber Security Risk Assessment on Industry 4.0 using ICS testbed with AI and Cloud | Semantic Scholar

Figure 3 from A Dual Threshold Secret Sharing Scheme among Weighted Participants of Special Right | Semantic Scholar

Bite-sized: 50 great short stories, chosen by Hilary Mantel, George Saunders and more | Short stories | The Guardian

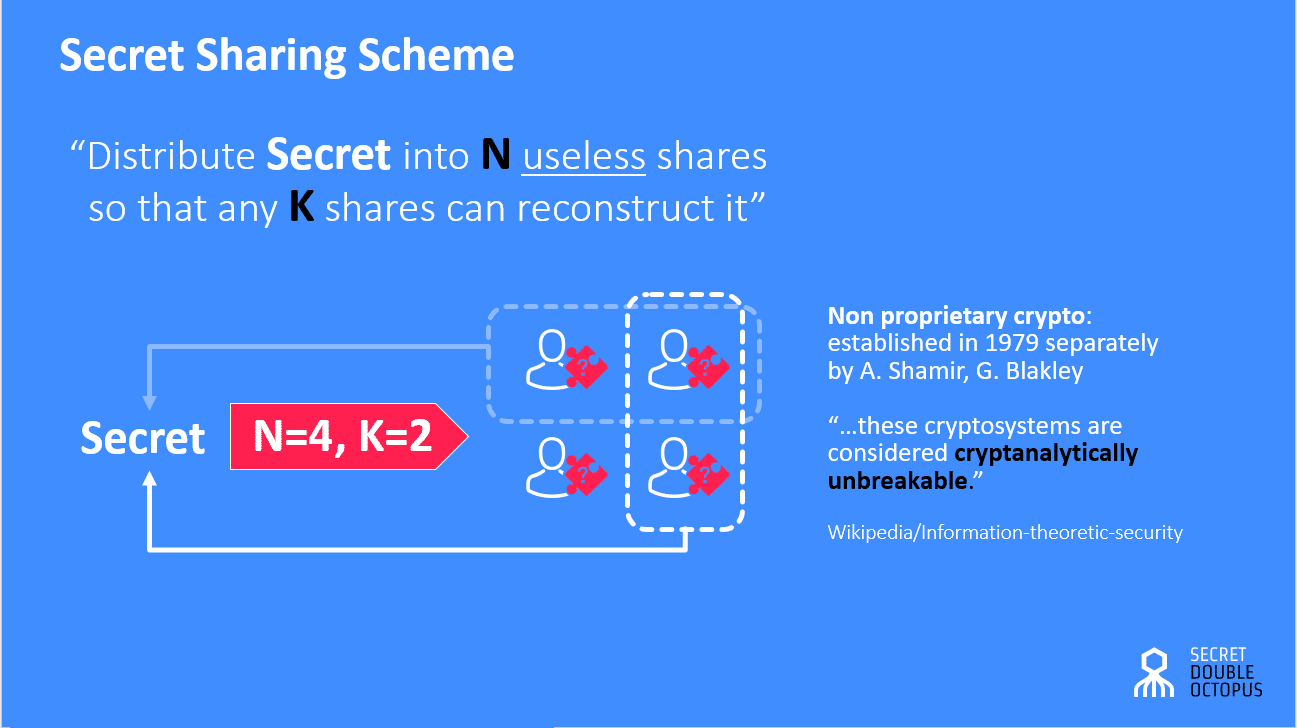
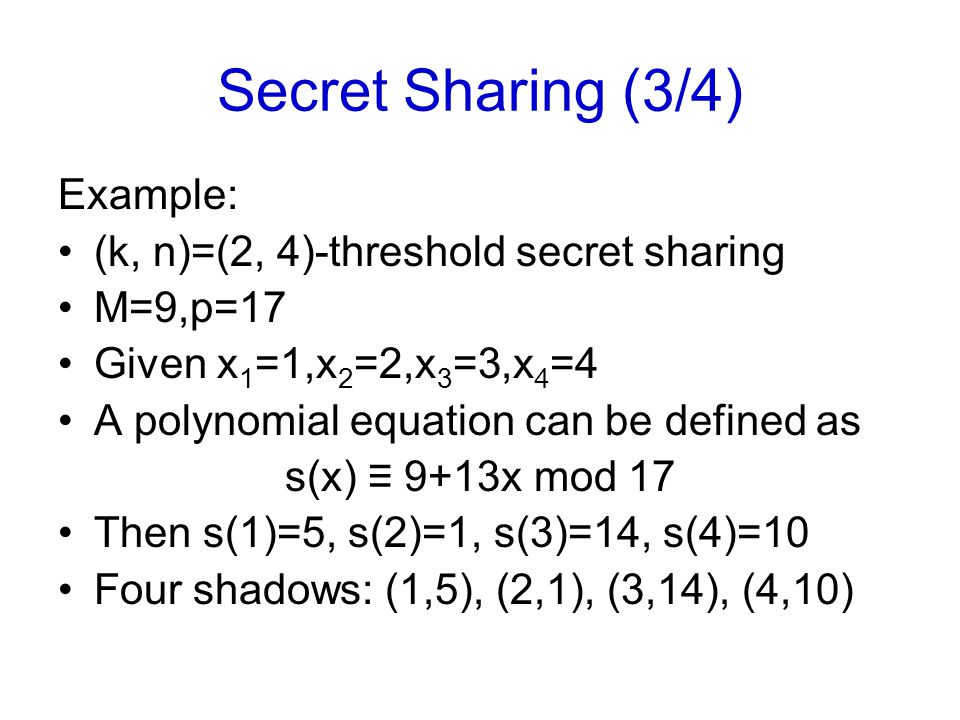
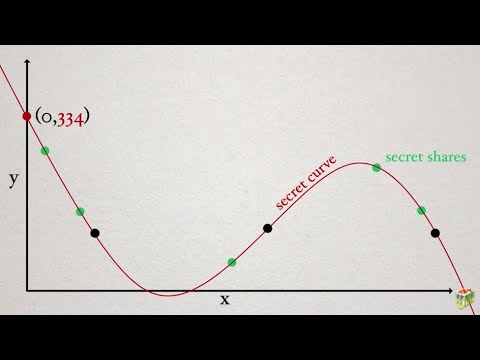
Distributing a Shared Secret amongst a Group of Participants using Shamirs Secret Sharing Scheme aka ssss

SETUP in secret sharing schemes using random values - Olimid - 2016 - Security and Communication Networks - Wiley Online Library

SETUP in secret sharing schemes using random values - Olimid - 2016 - Security and Communication Networks - Wiley Online Library

SETUP in secret sharing schemes using random values - Olimid - 2016 - Security and Communication Networks - Wiley Online Library









![PDF] Application of Biometric Key in Practical Secret Sharing for DNSsec | Semantic Scholar PDF] Application of Biometric Key in Practical Secret Sharing for DNSsec | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/9d617a3c9d82c2432d96075f798331f95055acdf/2-Figure1-1.png)