PDF) Bluetooth MITM Vulnerabilities: A Literature Review, Novel Attack Scenarios, Novel Countermeasures, and Lessons Learned

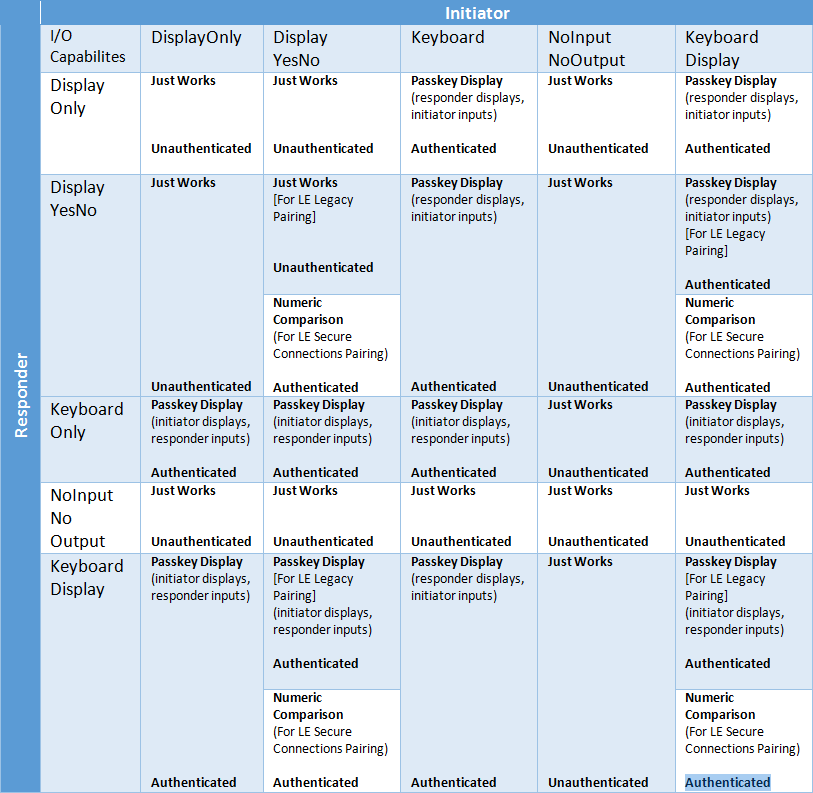
Bluetooth Pairing Part 4:Bluetooth Low EnergySecure Connections -Numeric Comparison | Bluetooth® Technology Website
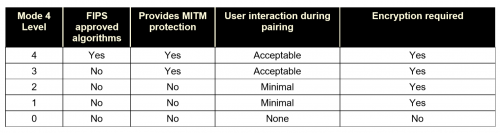
IWD2243 Wireless & Mobile Security Chapter 4 : Security in Wireless Ad Hoc Network Prepared by : Zuraidy Adnan, FITM UNISEL1. - ppt download